Encryption Key
Table of Contents Show
Importance of Encryption
Sensitive data (such as credit card numbers) that must be stored to the database are protected with Advanced Encryption Standard (AES) cryptography. AES is a keyed encryption – you need a secret password to encrypt and decrypt the data. Sensitive account data is encrypted within the database using a secret key. AbleCommerce introduces a new interface for managing this key so that your sensitive data cannot be read by anyone who does not know the key.
When you deploy AbleCommerce it does not have a key set. If you are storing credit card data it is important that you set the encryption key after deployment. You should change the key at least once per year.
Without the key, the data cannot be read. Maintaining the encryption key for AbleCommerce is an important task because it impacts the security of your data. As a merchant, you must ensure that users responsible for the encryption key sign a written statement that they understand and accept the duties and responsibilities as custodian(s) of the key. The key custodians should be fully familiar with the requirements of the PCI DSS. Also be sure to maintain appropriate key backups and store the backup keys securely.
Change your key regularly. Every 90 days is recommended. You should also change the key any time an employee with access to the key leaves your company. Always replace the key if you know or suspect it has been compromised by any means.
Change the Encryption Key
To change your key, all data in the database must be decrypted with the old key and then re-encrypted with the new key. This process can take some time depending on the size of your database; the estimated workload is shown. Once you initiate a key change, a progress indicator will be shown to let you know when the process is complete. Always ensure you have both a database backup and a key backup before initiating a key change.
From the menu, go to the Configure > Security > Encryption Key page.
Find the section named Change Encryption Key as shown in the example below.
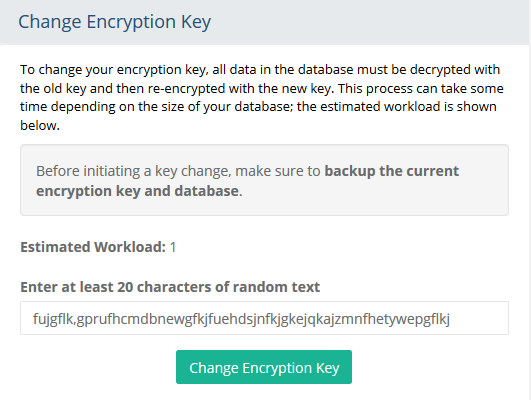
Enter some Random Text in the field provided. This will be used to help generate the secret key. You must type at least 20 characters; the more random the better.
Click the Change Encryption Key button to begin. Please wait for the re-encryption process to complete. It might take some time depending on the size of your database.
Have the system administrator restart the application pool for the website.
Backup the Encryption Key
To keep your key secure, it is securely stored apart from the database. In the event that you must restore your database to another location, it will be vital that you have this key. Whenever you change your key, download the key backup files and store them in a physically secure location. You need both backup files to restore the key.
From the menu, go to the Configure > Security > Encryption Key page.
Find the section named Backup or Restore Encryption Key as shown in the example below. If you have not created an encryption key, then you will see a message indicating this. Create an encryption key by following the instructions in the section above. Then you will be able to backup the key.
If you have created an encryption key, you will be able to backup the key as shown in this example.
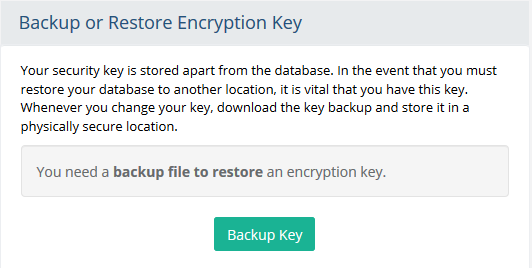
Click the Backup Key button to save your key.bin file. Place this file in a secure location, such as on a storage device and locked in a safe. Do not store the file on the server or any place where it is accessible to anyone besides the person responsible for its security.
IMPORTANT: Whenever you change the key it is very important to create a backup to an offsite location. If your web server crashes, the encrypted data in your database will be unrecoverable without a restorable key backup.
Restore the Encryption Key
If you need to restore your key, provide the backup file created in the prior section. The key currently being used will be replaced with the backup. No re-encryption takes place during this process, since presumably the existing data is already encrypted with the backup key you wish to restore.
When moving an installation to a different server, you will need to restore your encryption key by providing the recent backup file. If you have a newer encryption key already set, then the key currently being used will be replaced with the backup resulting in loss of data. Always use the latest key backup when performing a restore.
From the menu, go to the Configure > Security > Encryption Key page.
Find the Backup or Restore Encryption Key section as shown below.
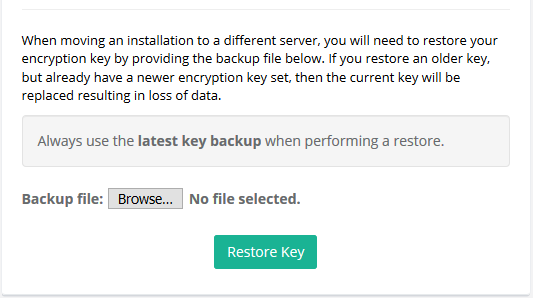
Select Browse... button next to Backup File. Find the file named "key.bin" to restore.
Click the RESTORE KEY button. You will have a chance to cancel or proceed with the action.
In a moment, you will see a message Key backup restored, if the task was successful.
Have the system administrator restart the application pool for the website.